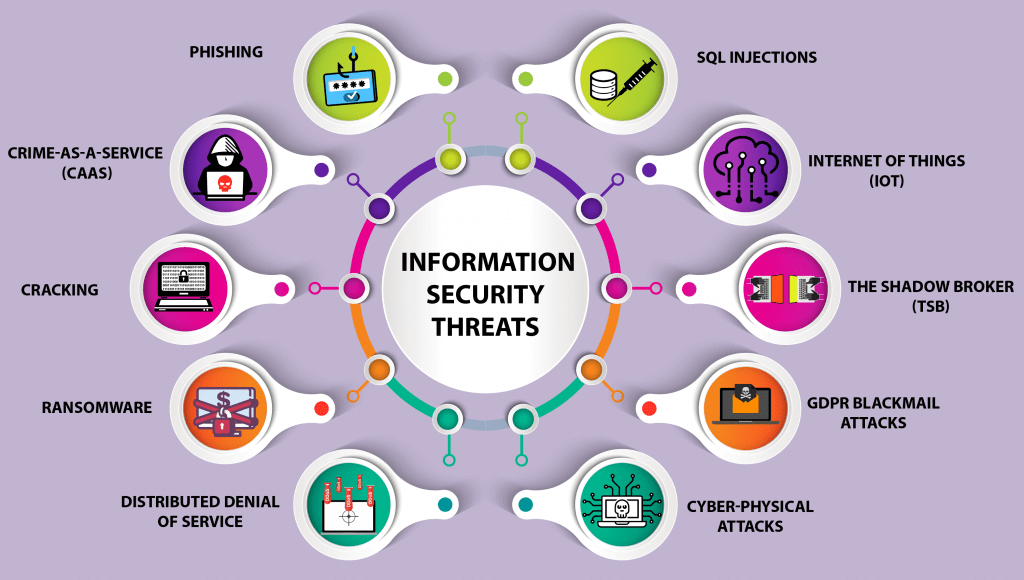
ISC Security Events on Twitter: "#IoT Security Risks! Top 10 #Security targets. Learn more about #CyberSecurity at #ISCEast @SIAonline Education. https://t.co/IcZFkaFfRP" / Twitter
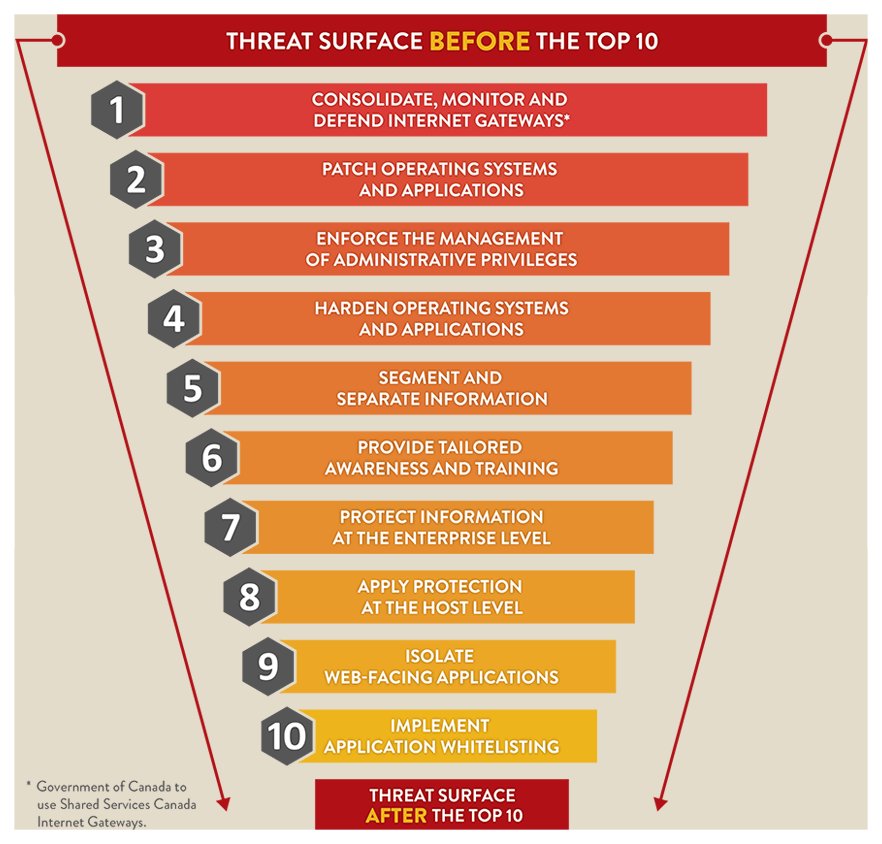
Canadian Centre for Cyber Security on Twitter: "The Top 10 Information Technology Security Actions are effective. Organizations that implement these recommendations will address many vulnerabilities and counter most current cyber threats ...

![Top Cybersecurity Threats [2023] Top Cybersecurity Threats [2023]](https://onlinedegrees.sandiego.edu/wp-content/uploads/2023/03/Top-Cybersecurity-Threats-in-2023-1024x582.jpg)